DCIM technology, through real-time data insights, confirms that assets are always on and protected

Now that companies have fully entered – and even embraced – the digital age, enterprises are forced to reconsider their business models and priorities. In this new extremely connected, yet broadly distributed world, business leaders must recognize and value the role that data processing plays in the modern customer experience. Regardless of where customers or employees are located, a business’ infrastructure must be capable of processing massive amounts of data with little to no latency if they wish to remain competitive in this new business environment. Data center infrastructure management (DCIM) can help with that.
Perhaps, the most effective way businesses are accommodating this newfound demand for data is by establishing edge computing facilities that take some of the load off their central data processing centers while also reducing latency of data transfers, regardless of the location of the end-user. For example, if a central data processing center is in Florida but has customers in Oregon, any actions taken by those customers on an app or website must travel all the way to Florida and back.
The distance of this data transfer alone would result in latency, which would cause lag for the customer experience. In this example, if someone was to establish edge computing facilities in California or Nevada the distance between the end-user and the processing center is much shorter which would make it much faster. In addition, there are considerations of data haul costs, data protection and fast computation processing that require data process functions to occur closer to the user and application. That is the value of edge computing.
Despite its benefits, the dispersed nature of edge computing can cause stress for engineers, maintenance techs and facility managers alike as they are unable to be on-premise at every single center to physically maintain and monitor each asset themselves. Furthermore, enterprises can have hundreds or even thousands of edge computing data centers, many of which are completely unmanned.
In order to ensure uptime, monitor and optimize energy usage and maintain the physical security of these edge facilities, facility managers must include data center infrastructure management (DCIM) tools in their edge computing strategy.
When DCIM was first introduced, it delivered capabilities such as real-time monitoring and task automation to reduce the hardware footprint and improve uptime in core on-premise data centers – making the facility’s administrator’s job significantly easier by driving new efficiencies.
Fortunately, there have been many improvements made to these tools over the last few years expanding on both the capabilities and the aforementioned benefits to facility managers. Next-generation DCIM is the next phase of data center management evolution and will further optimize resources by providing real-time visibility across distributed IT environments.
Evolution of DCIM
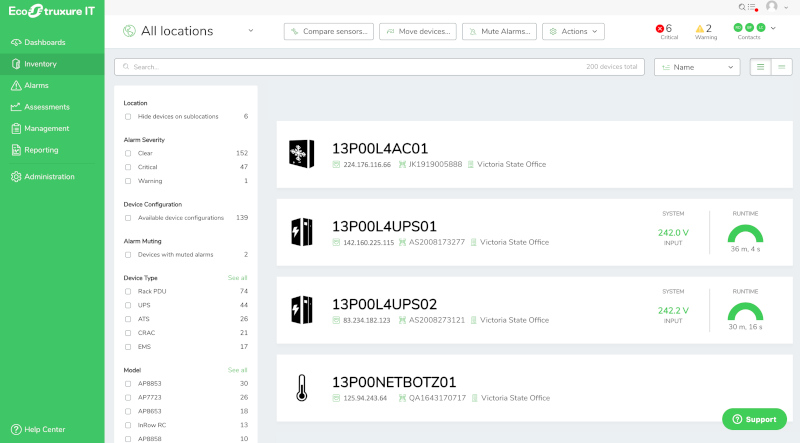
Modern data processing facilities are equipped with huge amounts of sensor-enabled equipment to provide insights into how efficiently they are operating. Managing the compute responsible for this massive amount of processed data is unrealistic and largely inefficient for modern facility managers. DCIM makes managing this information easier and more efficient by using software, hardware and sensors to monitor critical systems from a central dashboard in real time.
DCIM enables facility managers to have eyes on all assets at all times in all locations, which optimizes predictive maintenance, energy usage and back-up energy storage, while also maintaining physical security. Simply put, DCIM is the proactive eyes and ears on site, regardless of the location of the actual computing.
Predictive maintenance and energy usage
DCIM enables administrators to respond to problems more quickly – which prevents downtime – but in some cases an outage is unavoidable. With next-generation DCIM, however, the ability to prevent unplanned downtime increases substantially.
The main difference between DCIM and next-generation DCIM is that the new versions run in the cloud. As such, it is especially suited to running distributed IT environments that include centralized, regional edge and local edge computing environments.
One of the main benefits of cloud-based DCIM is visibility. Now, administrators get around-the-clock monitoring with full visibility of the environment anytime and anywhere. It also means being able to manage more with less and providing data center managers with greater knowledge (product information, historical data, product usage profiles, etc.), so they can have better operational control.
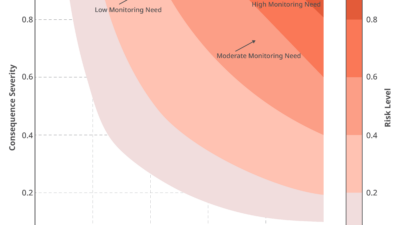
Analytics on power usage and environmental conditions are also factored into DCIM so administrators can make adjustments that reduce power consumption and protect equipment. And because the solution is cloud-based, it helps reduce footprint. Through data collection, next-generation DCIM tracks threshold violations and issues alerts when action is required to avoid an outage.
Another innovation that has been made to next-generation DCIM is the ability to not only flag potential failures, but also to deploy a trained technician to replace the faulty equipment the next day. Again, this new capability provides peace of mind for data center managers who have assets deployed at the edge and ultimately, increases resiliency and uptime.
Maintaining physical security
To continue the theme of omnipotence, monitoring environmental conditions enables administrators to essentially be in every room of their centers at the same time. Next-generation DCIM incorporates environmental monitors to provide real-time alerts for temperature, humidity, moisture, unlocked doors and windows, motion sensors, sound sensors, perimeter breaches and any other physical threats. As IT environments become increasingly distributed, physical security monitoring should be a non-negotiable part of any diverse IT strategy.
For example, instead of having technicians or security personnel patrol from room-to-room trying to manually spot security vulnerabilities, facility managers will be alerted of any anomalies in real-time and are able to pinpoint exactly what piece of equipment in which room needs to be addressed. This directly impacts a business’ bottom line as they don’t need to hire security personnel for each floor or area of their facilities.
It’s also important to note that threats to physical security are not always malicious human actors but can also be environmental threats. If a facility does not have smart security technology in place, DCIM can still be applied as it monitors environmental factors as well.
For example, one sparsely staffed co-location data center was alerted that a server room was running hot through their next-generation DCIM. When they deployed their engineer to investigate the issue, they discovered that the door was left open, and it was the middle of August. If this environmental threat was not monitored, this situation could have resulted in physical damage to their equipment and unplanned downtime.
At the end of the day knowledge is power, and when it comes to the efficient use of power that knowledge is discovered through real-time data insights. Thanks to these innovations in DCIM technology facility managers can sleep well at night knowing that their assets are always on and protected.