Successful network implementation starts with assessment of system and operations.

Reducing downtime, cutting costs and maintaining competitive advantages in production have always been primary goals for engineers. The onset of the Industrial Internet of Things (IIoT) will not change these objectives, but rather, it will alter how they are met.
Interconnectivity and the self-regulation of machines, Big Data and continuous improvement in processes will be critical for keeping industrial businesses up and running in this highly connected age. With the IIoT comes a variety of new possibilities and applications that businesses need to prepare and be ready for:
- Technologies will penetrate deeper into control systems, displacing legacy protocols and technologies, as well as hardwired systems.
- More (and smaller) things will be connected, and as this evolves, the number of things will grow exponentially.
- Maintenance won’t be reactive; rather, machines will be able to monitor their own condition and give early warnings when vital parts are about to fail.
- Information and operational technology integration will combine business systems with the data flowing into and out of industrial control systems. Big Data and analytics are a part of this trend.
- Data within control systems that have historically been only used for the operation of the system itself will also contain a wealth of useful information for running the business. This information can drive a wide range of new efficiencies, including better asset utilization, lower energy consumption, better supply chain management, predictive maintenance and manufacturing as a service, along with other cost savings and revenue enhancements.
Five critical steps to success
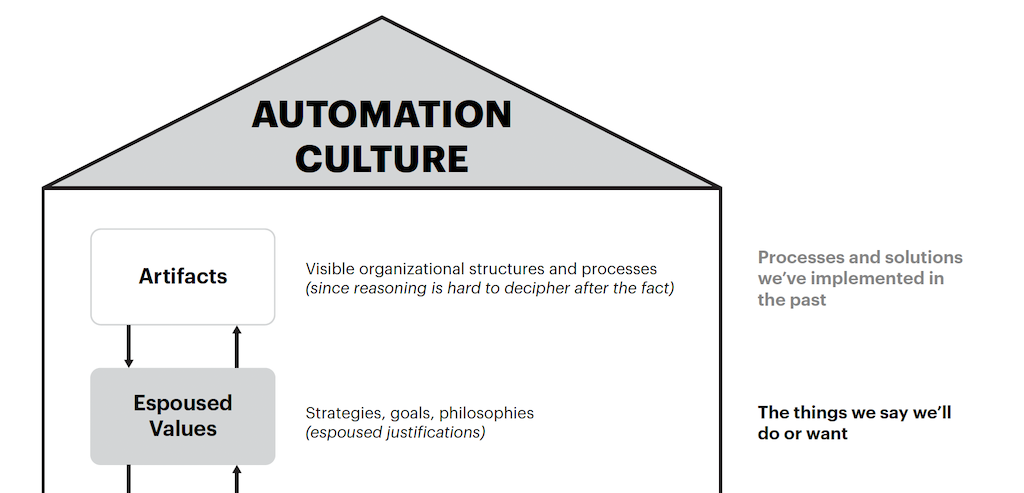
To tap the potential of the IIoT, companies need to move from today’s practices to those of tomorrow. This takes an evolutionary process that requires a strong industrial Ethernet infrastructure as the foundation for a system that can adapt to business needs. The following five-step process will help you prepare your network for the IIoT:
1. Assess and map the network: First, look at the current state of your business and decipher your goals for investing in the IIoT, whether it’s complete oversight of data, more flexibility or securing massive savings. Doing so will help outline a strategy and highlight the obstacles you need to overcome to get there. Once that’s set, you need to understand whether your network is ready for the IIoT. Start with an assessment, and ask yourself:
- What are the connectivity requirements of the current system? Do we need wired or wireless components?
- What bandwidth do we require? What expectations should we have for reliability?
- What environmental considerations should we keep in mind?
- What are the near-term goals for functionality and data exchange?
- What devices are currently on the network, and who owns each one? What is the role of each device, where does it live and what is it connected to?
- Which devices communicate with each other?
The end result of this stage should be an accurate map of your network infrastructure that will act as a baseline and help you track progress throughout the remaining steps.
2. Update the network to Ethernet: The goal of this step is to secure a solid network infrastructure that can handle the control, security risks and data required by the IIoT, both today and down the road. Look at existing legacy systems and see if they can be repurposed or upgraded and develop an integrated plan for migrating the technology. This includes sensors, actuators and electric motors that communicate using fieldbus. Making Ethernet the foundation, and using redundancy mechanisms to maximize network availability, will enable the network to better handle the demands and requirements of the IIoT.
3. Rethink network design to meet best practices: It’s very important to ensure your network meets established industry best practices and standards. This includes making sure there aren’t any built-in capabilities within the products that aren’t being used and that everything on the network is properly segmented into zones for protection against cybersecurity breaches. It’s also worth checking to see if wireless technology can advance the network by enabling an off-site workforce or remotely monitoring systems. This step is intended to benchmark the network against other market leaders to determine what constitutes a solid network design and will position teams to effectively navigate the new possibilities and challenges that come with the IIoT.
4. Ensure reliability, resiliency with Defense-in-Depth mechanisms: The extensive connectivity that comes with the IIoT makes companies more vulnerable to cybersecurity challenges. The best way to tackle network security is to take a layered approach and build security mechanisms within each level of the network, including the device level. Conduct a risk and vulnerability assessment to understand what risks exist, as well as the business impact and likelihood of their occurrence, then use the network map created in step one to identify what assets need the most protection. Focusing on protecting the businesses’ most critical assets first with regular network maintenance, assessments and audits is essential for success.
5. Continuously monitor for network changes: Technology is constantly changing and presenting new security threats, which is why continuously monitoring the network and making appropriate changes is vital. Leveraging real-time tools and alert mechanisms will help teams set up ongoing monitoring and troubleshooting so they’re always on top of risks. Conducting regular network maintenance, assessments and audits, responding to system failure alerts, establishing response protocols and following evolving best practices make a big difference in whether or not teams thrive in the face of the IIoT.
A case study in IIoT network design
Saudi Pharmaceutical Industries & Medical Appliances Corp. (SPIMACO) is a great example of a company that has successfully implemented and designed an IIoT-ready network. To provide a new network solution for its Al-Qassim plant, the largest pharmaceutical plant in Saudi Arabia spanning 150,000 square meters, SPIMACO executed the five-step plan with great success. Project priorities included increasing efficiency, ensuring state of the art security, and optimizing resiliency and enterprise-wide scalability.
SPIMACO was able to consolidate the plant’s medicine manufacturing machines into one network, with a centralized manufacturing execution system (MES). A total of 500 IP nodes were installed on the panels outside the hygiene area, such as corridors and walkable ceilings, to communicate with the central MES. The solution included a full Gigabit network, equipped with Layer 2 switches and Layer 3 routers installed over multiple rings, which created a highly available infrastructure that was able to expand as needed.
The complete network, including installation and testing in accordance with pharmaceutical industry standards, was ready in only five days, and the design gave SPIMACO the security, availability, reliability and scalability needed to fully take advantage of, and prepare for, the new frontier of the IIoT. The IIoT is certainly a journey, not a destination. A safe and solid network requires consistent attention as its needs and vulnerabilities will evolve over time. These steps are designed to give teams a strong foundation as they migrate to an IIoT-ready network and realize the benefits and challenges that come from a highly interconnected world. Nils Buecker is a project manager in Belden’s industrial IT division.