Cyber security for industrial networks is rapidly becoming necessary. In recent years, there have been numerous attacks where critical infrastructure, private industry and public sector control networks have been compromised or taken down. Protecting a control network is often more challenging than protecting a traditional office network.
Cyber security for industrial networks is rapidly becoming necessary. In recent years, there have been numerous attacks where critical infrastructure, private industry and public sector control networks have been compromised or taken down.
Protecting a control network is often more challenging than protecting a traditional office network. There is generally much less IT support on the plant floor than in an office. Plant networks also have older equipment running without support and non-patched operating systems. They need to avoid downtime that can occur when installing or updating firewall software or anti-virus programs.
Steps you can take to protect your control networks include setting up a firewall, segmenting the control network from the office network and taking some common-sense security steps.
Firewall protection
Implementing firewall protection secures your control network from unwanted and unnecessary traffic. A network firewall is hardware and/or software designed to protect network devices by inspecting each packet trying to pass through it. It denies or permits passage based on a set of rules.
Firewalls are grouped into categories based on rule complexity and traffic inspection level. These categories include access control lists, stateful inspection and application layer.
Access control list — Access control lists (ACLs) are the simplest firewalls. They inspect IP addresses bidirectionally. ACLs may also allow filtering on basic protocol choices such as TCP or UDP. You should be very explicit in setting up your rules. For example, to allow a PLC and an HMI to communicate, you must provide a rule that covers PLC-to-HMI and a rule that covers HMI back to PLC. ACL-based firewalls generally have the least latency because they evaluate only basic IP header information. They are still vulnerable to certain types of attacks such as spoofing.
Stateful firewalls — Stateful firewalls add a level of protection beyond ACLs without a significant increase to latency or cost. They still allow bidirectional IP header filtering. They also allow filtering on specific application layer protocols such as http, ftp, Modbus/TCP and EtherNet/IP.
Stateful firewalls also keep track of the connection state of the traffic flowing through them. Unlike ACLs, you don’t need to configure separate rules for your PLC and HMI to talk to each other. Create a rule allowing the PLC to talk to the HMI, and the firewall notes that you established a connection to the HMI’s IP address. The stateful firewall can also protect against spoofing and other attacks where invalid IP addressing is used.
Application layer firewalls — An application layer allows deep packet inspection; you also see what the packet contains, allowing you to filter out certain types of content within otherwise valid packets. However, the inherent latency is not compatible with typical industrial applications, where tens of milliseconds can make a difference.
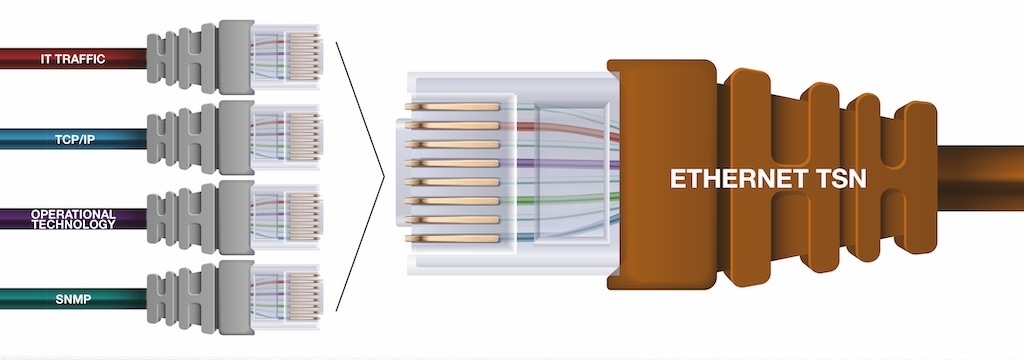
Control network segmentation
Segmenting your control network from the office network provides further protection. This is done by using a router. Available for less than $1,000, a router keeps broadcast traffic such as ARPs off the control network. Of course, the router still allows communication between the control and office networks, but it will allow you to manage it better.
Common sense
Finally, don’t forget to take simple security precautions such as:
-
Using strong passwords (6+ character, mix of letters and numbers)
-
Auditing who has access and to what on the network
-
Logging any configuration changes to verify who is doing what.
-
Treat access to your control network the same way you treat access to your credit card information; your network will be much more secure.
Securing your network is not a one-time task; it is an on-going process that you should revisit frequently to keep up with emerging threats. Take the steps needed to protect your network to ensure that your data, processes and business are safe.
Author Information Dan Schaffer is a product marketing lead specialist for Phoenix Contact. He has more than 10 years experience as a network engineer, specializing in troubleshooting and design.