As industry starts to engage in digital transformation programs, engineers tasked with managing this change are running into several challenges.

Digitalization of the industrial sector has begun in earnest and as smart and IoT-enabled technologies become more prevalent throughout all manufacturing sectors, the growing influx of data has presented challenges for information technology (IT) and operations technology (OT) professionals.
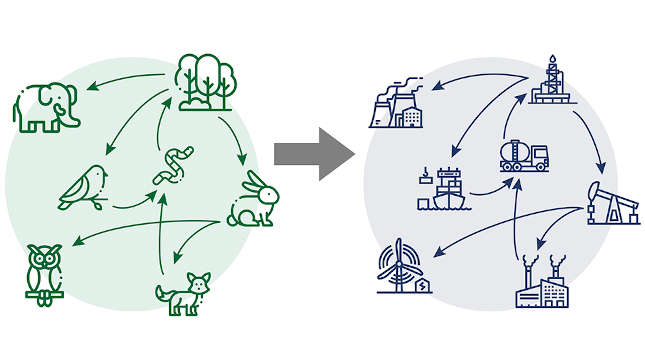
As the Industrial Internet of Things (IIoT) becomes more commonplace, IT and OT are beginning to overlap which presents a host of challenges. “While industry understands the potential offered by big data and the challenges that come with collecting and analyzing data, there is an added layer of complexity when it comes to managing this data and parsing through it in beneficial ways for both IT and OT professionals,” said Joe Gerstl, director of product management for manufacturing software at GE Digital. “Often, the challenge is as simple as IT and OT not speaking the same language – they often have a different set of guiding principles, goals and focus areas that drive the decisions they make.
When data is collected,” Gerstl said, “it is aggregated like a spider web where each group collects, analyses and monitors a given set of data points. Software products can help aggregate this data to ensure that both IT and OT professionals have it available at their fingertips throughout the factory floor and within their network of facilities. Data needs to be aggregated, put into context and visualized for all – so that professionals don’t need to wade through impossibly large data pools to infer the insights they need.”
“Today’s software and storage solutions are advanced enough to organize data, output automated reports and create digital twins to support IT and OT needs alike. Further, standardizing data capture, analysis and output provides greater transparency and understanding among peer sets by making information more manageable and easily available. As digital transformation programs continue to evolve, the potential for true IT/OT convergence, streamlined business operations and optimized production increases.”
Right time, right place
According to Benedikt Rauscher, head of global IoT/Industry 4.0 projects at Pepperl + Fuchs, one of the biggest challenges relating to the digital plant migration is getting data at the right time from the right place and to structure it in such a way so the data can be processed efficiently.
“Getting this right demands concepts for digital connectivity for both new installations (Greenfield) as well as for the refurbishment of existing plants or machines (Brownfield) and this requires the implementation of ruggedized IT-technologies on the shop floor,” he said.
Today’s digital communications protocols already provide identity, status and diagnostic data as well as remote configuration functions and utilizing these technologies to their full potential is a vital step in the digital transformation.
“The first challenge is to implement a digital communication infrastructure which makes identity, status and diagnostic data available in IT systems natively and without additional cost and the second challenge is to get that data structured in the IT system generically and independently from the underlying communication systems,” Rauscher said. “In brownfield plants it is necessary to set up communication paths in parallel to the existing 4-20mA loops to connect the field devices to IT systems and cloud platforms.”
Rauscher believes as IT and OT converge, technologies that enable protocols and standards from the office world to be used at the field level are vital. A new physical layer, Ethernet-APL, provides a fundamental infrastructure for this. It allows long cable distances and provides protection methods common for explosion hazardous areas. This physical layer has the potential to be the connection technology of the future for field devices.
Ethernet-APL is a two-wire-based advanced physical layer for Ethernet, intended for the fields of process automation and process instrumentation in remote and explosion-hazardous locations, enabling field devices to be deployed with additional functions and without the need for protocol translations. A project team consisting of specialists representing three networking organizations and 11 automation vendors are working cooperatively on the interface, which also incorporates the specifications outlined in NAMUR Recommendation NE168 (Requirements for a field level Ethernet communication system).
Supporting connectivity
Brendan O’Dowd, general manager for the industrial automation group at Analog Devices, believes the critical, enabling element of Industry 4.0 is an integrated communications network which can support connectivity throughout the factory.
“We are now seeing legacy communication protocols between sensor nodes and PLCs giving way to ultrafast industrial variants of the Ethernet protocol and this is enabling the increased integration of OT infrastructure in the factory with IT across the enterprise,” he said.
This, according to O’Dowd, means machine builders need to future-proof their system implementations, to enable them to support the industrial Ethernet protocols in use today and the emerging time-sensitive networking (TSN) variant of Ethernet, which is looking likely to become the standard wired networking technology for real-time industrial communications.
Security issues
Every move towards a more digitized, connected factory also increases the threat of cyber-attack, so security is a crucial priority when evaluating Industry 4.0 initiatives. Balancing real-time data with ensuring a device doesn’t get hacked is a serious challenge. While TSN can help overcome denial of service attacks by providing a robust set of traffic policing choices, it does not help with authentication or tampering with data.
“Taking a layered approach to security allows real-time data to be processed without interference,” O’Dowd said. “Optimizing security requires that instead of thinking about the requirements of any particular device or end point, a system-level approach is taken. In this way security can be delivered in a variety of ways throughout the system– within edge devices, controllers, gateways, or further up the stack. Before focusing on the how at any given point in the network, systems specifiers should be focused on questions of where and how much.”
O’Dowd said such an approach should consider the threat level at each point as well as the cost of countering the threat, with a view to adding effective security with the fewest trade-offs in power, performance, and latency. “A layered approach will result in a superior overall security posture,” he said.
Continuing on the subject of network security, Ivana Nikic, product marketing engineer – industrial Ethernet at Moxa highlights that, traditionally, industrial control system (ICS) networks have been physically isolated and not directly connected to the Internet, so have been almost immune to cyberattacks.
“When an interconnected factory starts connecting its internal systems to external systems it puts both IT and OT operations at risk,” she said.
Problems could include a single-point consideration without a system-wide view and inexperience which causes problems for management. Nikic suggests that this could be managed with a 3-layer security architecture based on the industrial standard IEC 62443.
“It should offer visualized management for security audit and monitoring, defense-in-depth protection for ICS with a secure network infrastructure, and hardened devices with embedded security functions,” she said.
This article originally appeared on the Control Engineering Europe website. Edited by Chris Vavra, production editor, Control Engineering, CFE Media, [email protected].